Centrally Manage Resource Permissions with Authing
Reduce Development and Operations Workload
step 1
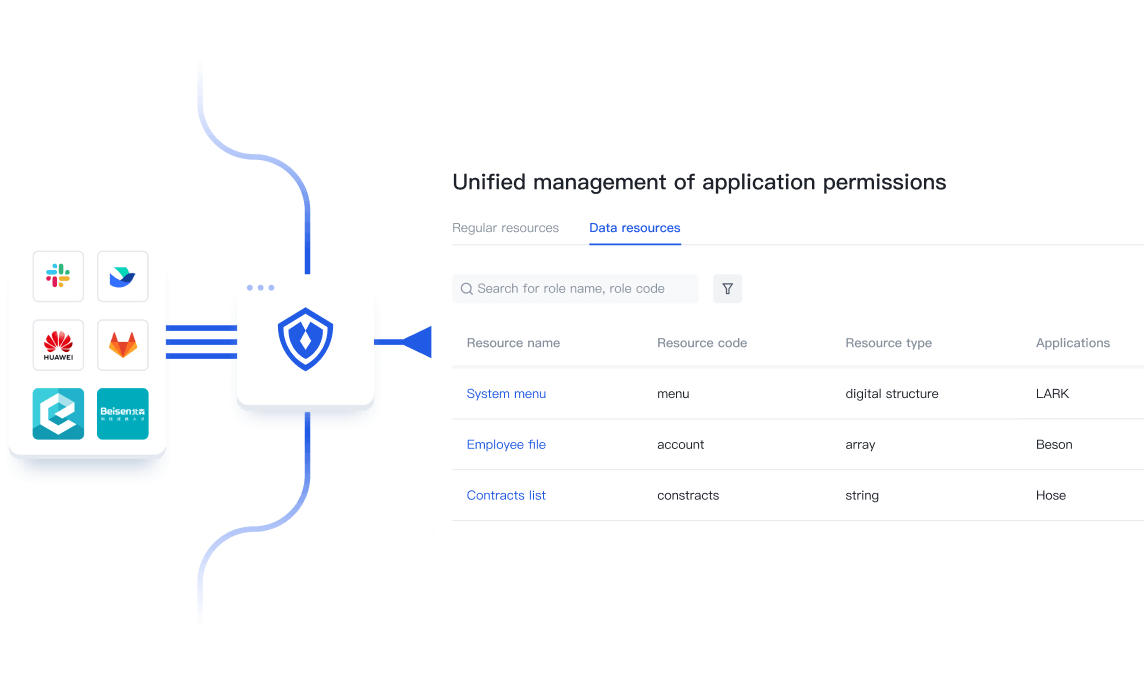
Fast integration to Authing for unified rights management
With Authing, organisations can easily integrate multiple disparate applications into a unified backend, split functionality into resources, and centrally control resources under each application.
step 2
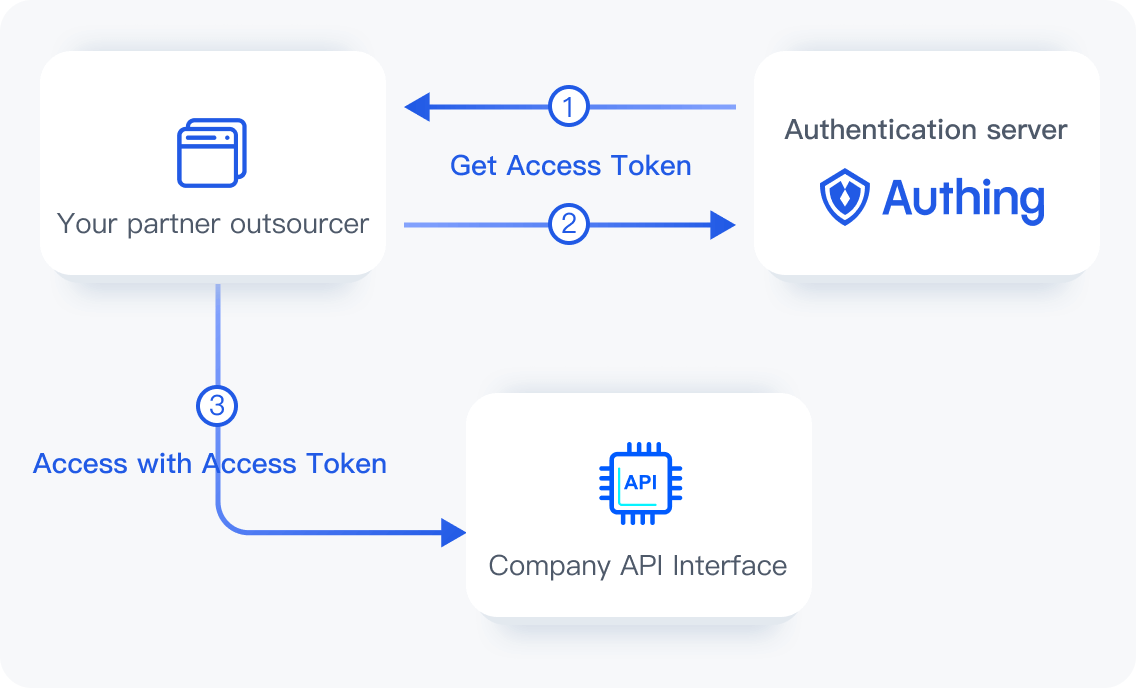
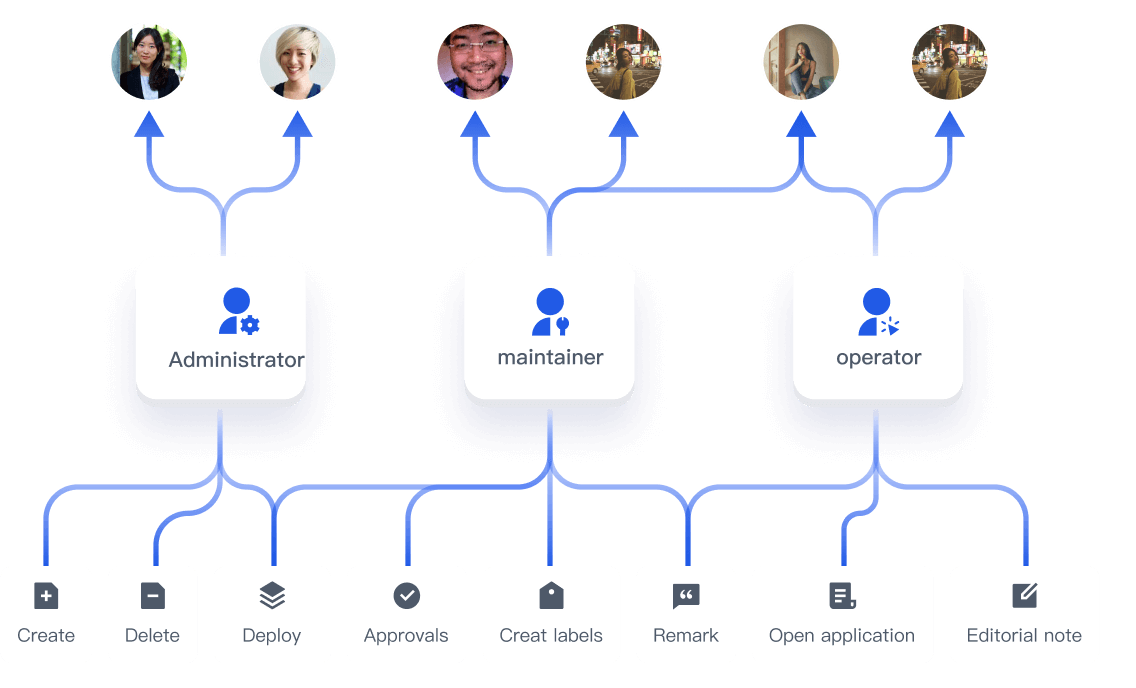
Customising resources, operations and roles
Authing supports enterprises to create APIs, menus and other resources according to their needs, define the corresponding resource operations, and the roles of the subjects that are granted permissions.
step 3
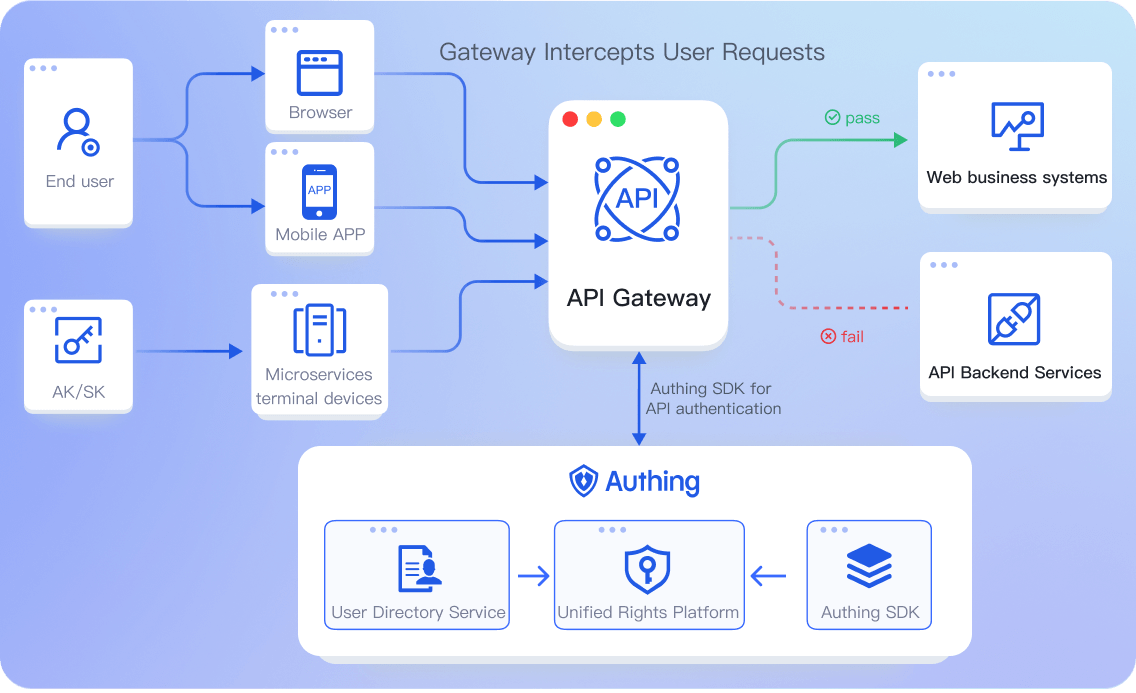
Easily Implement Granular Authorization Policies by Assigning Resources and Operations to Roles
Role-based access control
- What is RBAC
- Scenario: Small and Medium- sized Enterprises
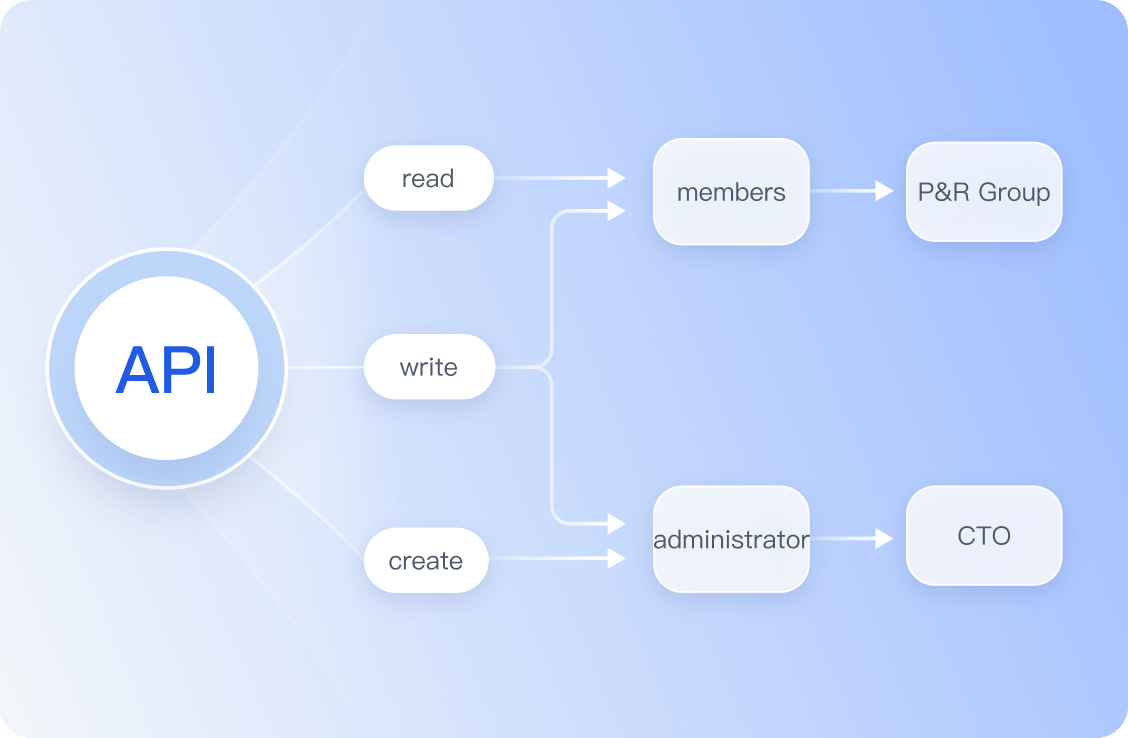
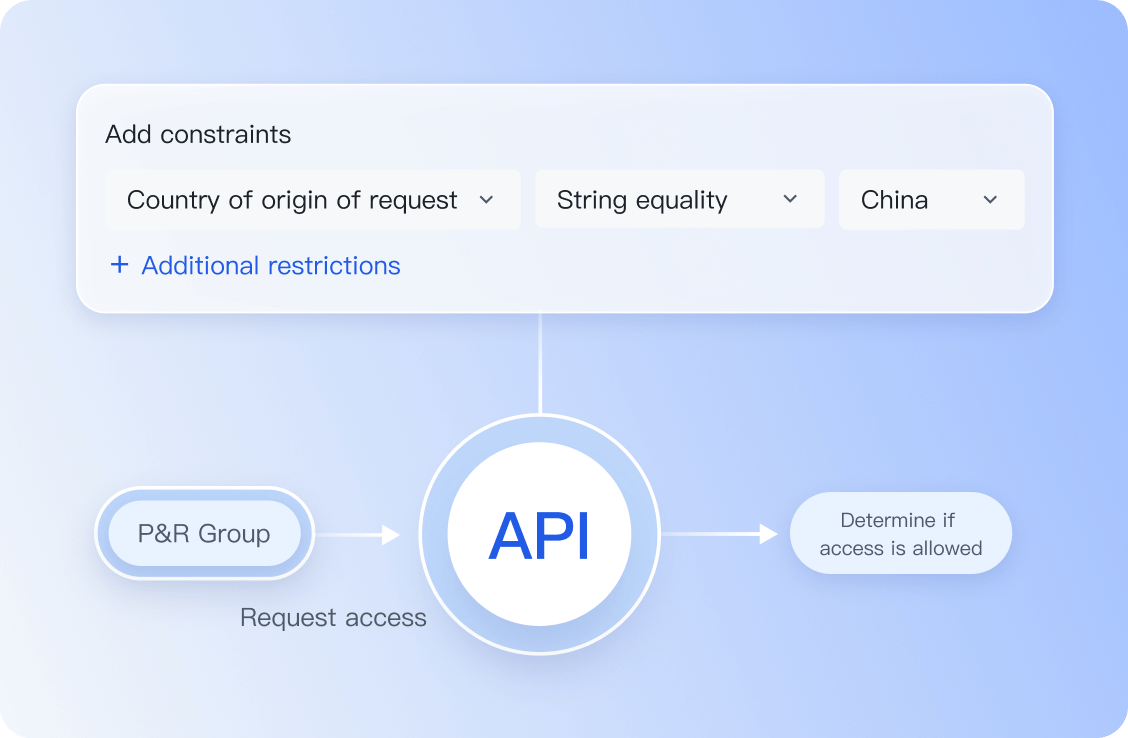
Attribute-based access control
- What is ABAC?
- Scenario: Large Organisation
step 4
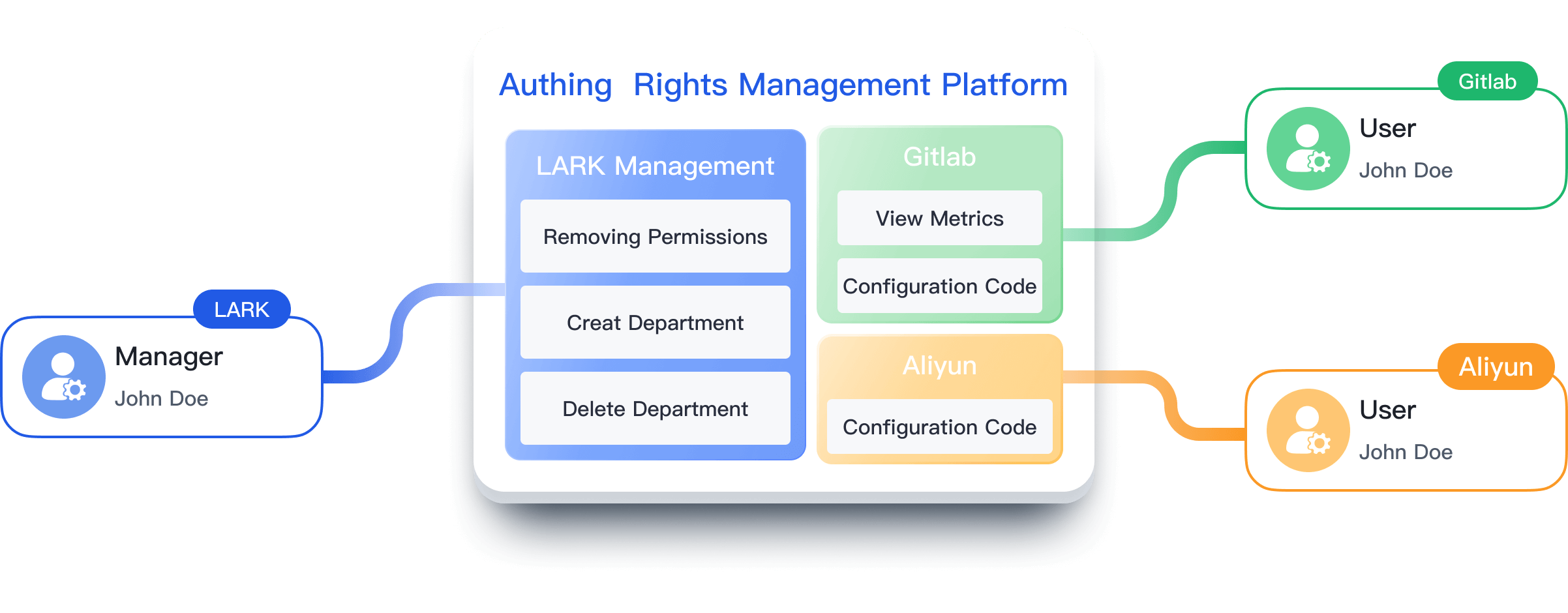
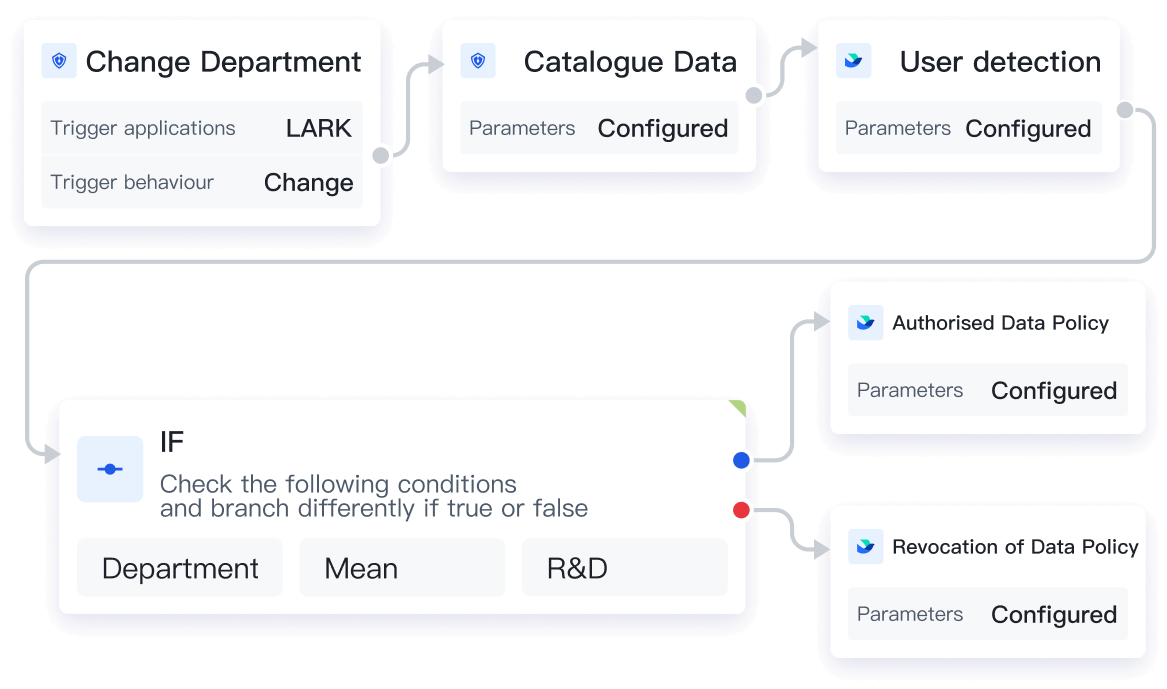
Automate processes to reduce manual inefficiencies
By integrating permission policies with Authing's identity automation, changes in employee or organizational structure can automatically initiate permission management, reducing costs and data leakage risks.
step 5
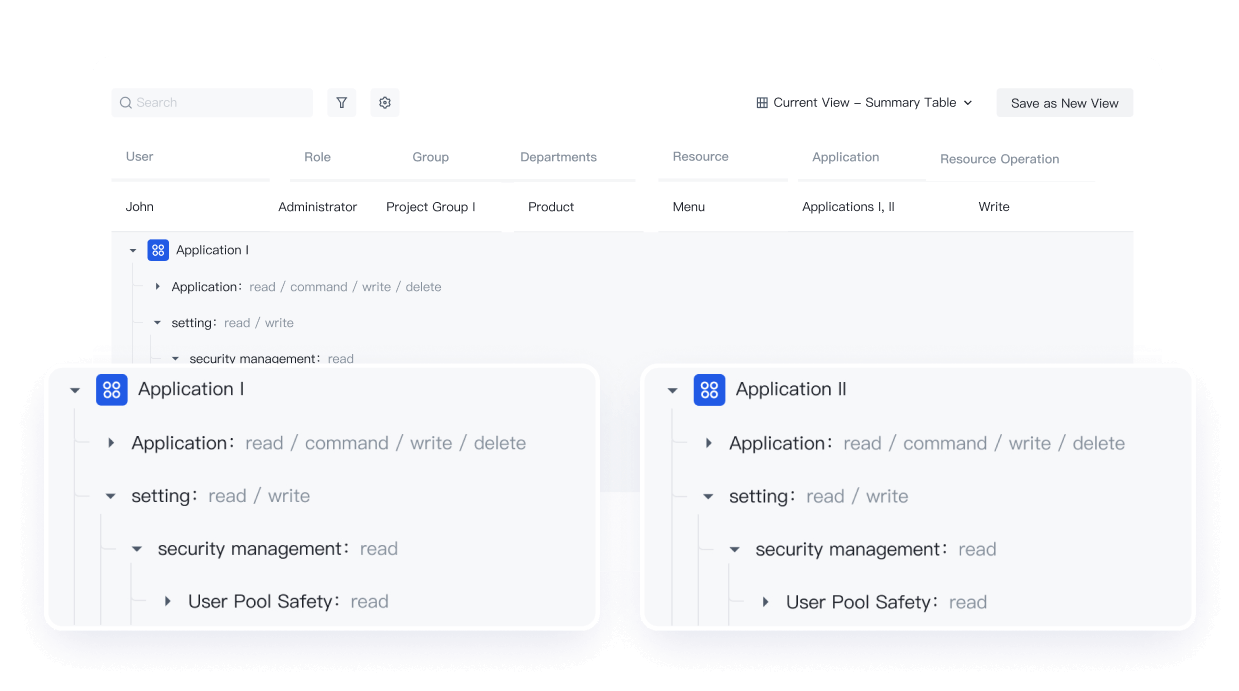
Generate permission views with one click
Authing provides a visual, global view of permissions by user, showing the user's resource permissions and associated policies under different applications for easy auditing after the fact.