为什么选择 Authing 替代 Keycloak?
基于开源软件自研身份认证与管理系统,仍需投入大量的技术成本,且有较高的安全风险
使用 Authing
享受开箱即用的身份认证产品
安全合规完善
Authing 有完善的安全防护策略,能依照企业需求进行设置;也拥有 ISO、三级等保、GDPR 等数据安全认证,能满足中国大陆的合规要求。
投入成本低
Authing 提供成熟的 IDaaS 产品,同样支持单点登录、身份认证、权限管理等功能,配合完善的技术文档,能大幅缩短企业的开发时间。
运营维护轻松
Authing 作为企业级软件,经常升级功能、修补漏洞,无需企业自行维护;产品不仅容易上手,还有丰富的实施经验能帮助企业更高效地进行建设。
客户服务活跃
针对企业客户,Authing 提供专属的客户成功经理,平均能在 20 分钟内进行响应;针对个人开发者,也有完善的开发者论坛,为用户答疑解惑。
使用 Keycloak
面临开源软件的隐藏缺陷
安全合规不符
开源软件的代码有机会被黑客直接访问,并且较难依据企业的网络安全情况,定制合适的 IAM 安全策略;也较难满足中国严格的安全合规要求。
研发成本高
开源软件不是完全免费的。企业基于 keycloak 开发身份认证与权限管理系统,仍需投入大量的技术成本,才能确保系统符合业务需要。
运营维护困难
开源软件修复 Bug 的方式,容易使源代码出现结构问题,导致企业难以维护;对于特定技术问题,也较难在开源社区中快速找到可靠的解决方案。
售后服务缺乏
Keycloak 属于免费的开源项目,没有固定的开发者支持,也没有迅速响应的客户成功服务。若遇到紧急的问题,安全和效率方面缺乏保障。
使用 Authing,快速上线完善的身份体系
与 Keycloak 相比,Authing 的商业支持更加完备,建设经验也更为丰富,能真正地帮助企业提升身份管理的 ROI。
| 功能 |  |  |
|---|---|---|
OAuth 2.0, OIDC, SAML, AD/LDAP 等 | 目前只支持 OIDC 和 SAML 2.0 | |
Web 和移动应用程序的身份验证 | ||
审核日志 | ||
自定义用户数据 | ||
密码泄漏检测(实时) | ||
语言国际化 | ||
强数据隔离 | ||
自定义密码加密算法 | ||
高级许可和合规管理 | ||
暴力破解检测 | ||
连接自定义社会化登录 |
选择高安全、高性能、高生产力的身份产品
- 高安全
- 数据存储使用 AES-256 算法加密;通过 SSL/TLS 协议加密传输;使用 KMS 管理密钥,密钥定期轮换。
- 7x24 小时的安全应急响应;两地三中心备份,保证灾难时快速恢复。
- ISO、等保三级、数据保护条例等多项认证。
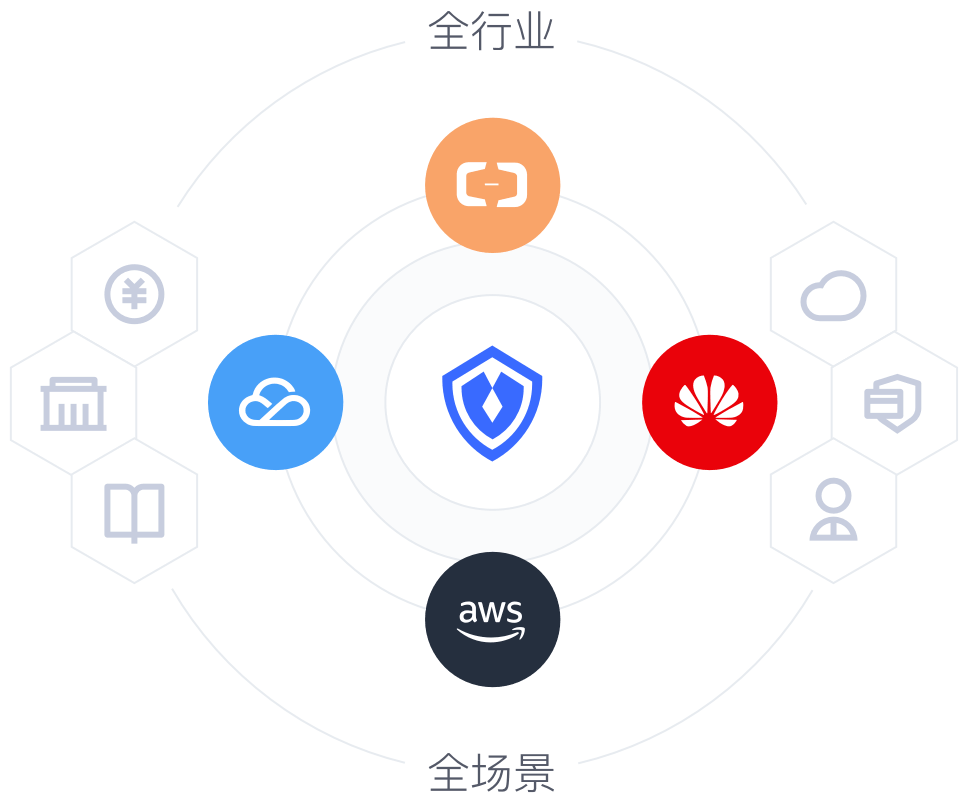
- 高性能
- 云原生:采用 Kubernetes 容器化技术,支持分钟级别弹性扩容,可支持亿级别用户认证访问场景。
- 云中立:兼容用户的云环境,不被原有的云厂商捆绑。
- 高生产力
- 开发者友好:提供丰富登录、认证、授权 API/SDK,降低研发成本。
- 快速集成 2000+ 主流应用,简单、高效的建立身份中台。
快速集成 五分钟实现
单点登录、认证授权、权限管理等功能