Scene profile
For companies competing in "Borderless and Digital World", the protection sensitive system and customer confidential data are critical. However, the current network security situation is not optimistic. When customer data is abused or stealing due to improper importance, companies will not only suffer business losses, but also facilitate huge compliance fines and other legal penalties.
According to the data in 2016-2019, China's IT expenditure accounts for the world's proportion and GDP, the degree of digitalization in Chinese companies is in high-speed growth. When the company has gradually recovered from the 2020 global epidemic situation, they will also face a large number of IT project backlogs, however, funds used to complete these projects are limited.
Therefore, building identity cloud IDaaS will help companies achieve digital transformations faster, reduce financial burden, and effectively avoid the development of manufacturing disorders to increase unnecessary costs.
Authing has helped 20000+ companies and developers to build standardized user identity systems
Perfect identity service
The traditional IAM account center has weak operational capabilities, difficult to meet large organizations in business, while iDaAS's multi-tenant operation platform and automation workflow (Workflow) can easily enhance corporate operation efficiency.
Reduce corporate development costs
Subscribe Authing will save the cost of building an identity management system and mitigate the burden of future repairs upgrades. The liberated human material can let the development team focus on the core business, develop new growth space for the innovation capacity of the company, but also speed up the delivery of products.
Improve operational management efficiency
The interior of large enterprises and organizations will usually be divided according to dimensions such as "Region", "Department", and different services often need to ensure independence, Authing Identity Cloud Utilize multi-tenant technology to help companies solve the problem of business and data.
Improve identity safety
Dynamic tokens, face recognition, etc. MFA function, comprehensively improve system access security and ensure user access security.
Improve system scalability
Once you purchase an identity management API development kit, the development team can integrate the application you need on the platform, no need to repeat the construction, purchase identity management plan, and is very friendly to developers.
List of features required to be included in standard identity cloud
The following is a list of functions that a standard identity cloud IDaaS needs to include. Of course, each enterprise has its own unique organizational form and business model.
Primary function
Secondary function
Explain
Unified account
User management
User batch import and export
Add / delete / modify / check the user account number item by item / batch
User attribute management (basic field + user defined field)
User status management (enable / unlock / disable / activate, etc.)
User password reset
Organization and management
Multi level organization structure tree
Organization and management
User group management
User group creation / query / deletion, etc
User group attribute management
Directory synchronization
Account synchronization (upstream synchronization)
Unified certification
Authentication source management
It supports authentication source configuration, supports adding enterprise wechat, ad authentication source and LDAP authentication source; supports user-defined authentication source, including authentication source based on openid, SAML and CAS protocol.
Authentication method
Support Adaptive MFA, including account name / password, OTP, QR code, social login authentication, etc
Authentication configuration
Support different authentication factors for different applications
Unified application
Application management
Support application pre integration; support the creation of custom applications (openid connect, formpost, SAML2.0, CAS, oidc and other standard protocols)
Single sign on
Support the configuration of SSO for applications
Account number supply
Support the synchronization of accounts, institutions, etc. to the application system
SaaS service access capability
Supports integration of third-party SaaS or enterprise self-built applications through OIDC, SAML, CAS, LDAP, AD and other standard protocols
Tenant-level app access
Support access to different applications according to different tenants of IDaaS identity cloud;
Workbench integration
Support enterprise wechat workbench; support adding workbench
Unified authority
Authority management
It supports application level authorization and RBAC based authorization
Permission configuration
Support authorization based on user / user group / organization
Permission synchronization
Support the synchronization of application permissions
Unified audit
User action log
Support the query and export of user operation log
Administrator operation log
Support query and export of administrator operation log
Security management
Administrator configuration
It supports the creation and deletion of administrators / administrator groups, and supports the configuration of different administrator roles
Security policy
Support password policy configuration, including password strength settings, password reset settings, login security settings, etc
Operation and maintenance & operation management capability
IDaaS tenant operation platform
The enterprise operation center supports centralized management of all tenants, applications, orders, etc. in the identity cloud; core data visualization
IDaaS operation & maintenance platform
One-click deployment belongs to the IDaaS platform, and system operation and maintenance, data monitoring, and service upgrades are all under control
Unified account
User management
User batch import and export
Add / delete / modify / check the user account number item by item / batch
User attribute management (basic field + user defined field)
User status management (enable / unlock / disable / activate, etc.)
User password reset
Organization and management
Multi level organization structure tree
Organization and management
User group management
User group creation / query / deletion, etc
User group attribute management
Directory synchronization
Account synchronization (upstream synchronization)
Unified certification
Authentication source management
It supports authentication source configuration, supports adding enterprise wechat, ad authentication source and LDAP authentication source; supports user-defined authentication source, including authentication source based on openid, SAML and CAS protocol.
Authentication method
Support Adaptive MFA, including account name / password, OTP, QR code, social login authentication, etc
Authentication configuration
Support different authentication factors for different applications
Unified application
Application management
Support application pre integration; support the creation of custom applications (openid connect, formpost, SAML2.0, CAS, oidc and other standard protocols)
Single sign on
Support the configuration of SSO for applications
Account number supply
Support the synchronization of accounts, institutions, etc. to the application system
SaaS service access capability
Supports integration of third-party SaaS or enterprise self-built applications through OIDC, SAML, CAS, LDAP, AD and other standard protocols
Tenant-level app access
Support access to different applications according to different tenants of IDaaS identity cloud;
Workbench integration
Support enterprise wechat workbench; support adding workbench
Unified authority
Authority management
It supports application level authorization and RBAC based authorization
Permission configuration
Support authorization based on user / user group / organization
Permission synchronization
Support the synchronization of application permissions
Unified audit
User action log
Support the query and export of user operation log
Administrator operation log
Support query and export of administrator operation log
Security management
Administrator configuration
It supports the creation and deletion of administrators / administrator groups, and supports the configuration of different administrator roles
Security policy
Support password policy configuration, including password strength settings, password reset settings, login security settings, etc
Operation and maintenance & operation management capability
IDaaS tenant operation platform
The enterprise operation center supports centralized management of all tenants, applications, orders, etc. in the identity cloud; core data visualization
IDaaS operation & maintenance platform
One-click deployment belongs to the IDaaS platform, and system operation and maintenance, data monitoring, and service upgrades are all under control
How Authing support various scenarios
API security
Improving API security and ensuring compliance with internal and external partner use cases in a zero trust environment can be challenging. Authing provides end-to-end API security and management based on an open standards approach.
For users
Easily protect and expose your API by supporting all OAuth 2.0 authorization flows and fine-grained scope and permissions, so as to expand the market scope and provide a better user experience.
For applications and systems
You can easily facilitate secure communication between the API and non interactive external clients and internal APIs with the touch of a switch.
For enterprise developers
Enable third-party application servers, APIs and system backend to issue authenticated requests to your APIs, while always maintaining control over fine scope and permissions.
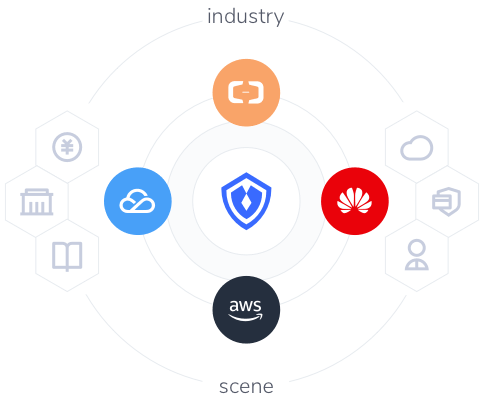
Numerous compliance certifications to ensure identity security
There is no doubt that customer data security and compliance are the primary considerations of most companies. Authing has the most advanced security built into the product, so you don't have to worry about the security of your users and business.
Industry standard agreement: Improve the consistency and continuity of business operation and execution by adopting identity platforms that support industry certification standards such as OAuth and openid connect.
Compliance and certification: Authing has a number of domestic and international compliance certifications, including the DJCP Level 3, SOC 2, GDPR, ISO 9001, CCPA, PCI, HIPAA and FERPA, etc., vowing to protect every user & business.
Public and private clouds: Host your application in authoring's public cloud, our private cloud or your AWS environment. Our highly available multi tenant cloud service can handle a large number of transactions every day.
Learn more
Universal Login
The guard helps developers shield themselves from many of the implementation...
Mobile Number Verification
Relying on the official real name user information of wechat, users can...
Custom Database Connection
When you want to ensure data security or smooth migration of users, please use Authing...
Integrate Authing in 5 minutes
Single sign-on, authentication, authorization management, etc.